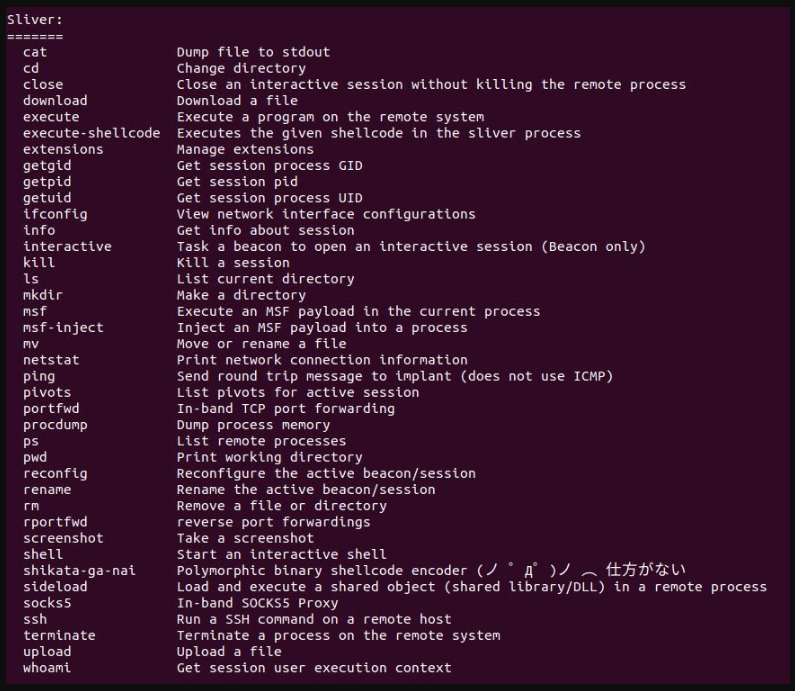
Last summer, threat actors began using Sliver as an alternative to Cobalt Strike, employing it for network surveillance, command execution, reflective DLL loading, session spawning, and process manipulation.
Recently observed attacks target two 2022 vulnerabilities in Sunlogin, a remote-control software developed by a Chinese company, according to the AhnLab Security Emergency Response Center (ASEC).
Attackers exploit these vulnerabilities to compromise a device, then use PowerShell scripts to open reverse shells or install other payloads, such as Sliver, Gh0st RAT, or XMRig Monero coin miners.
Attacking With a Malicious Driver on Board
With readily available proof of concept (PoC) exploits, the attack exploits the CNVD-2022-10270 / CNVD-2022-03672 RCE vulnerabilities in Sunlogin v11.0.0.33 and earlier.
Intruders exploit the flaw to disable security products before deploying backdoors using an obfuscated PowerShell script.
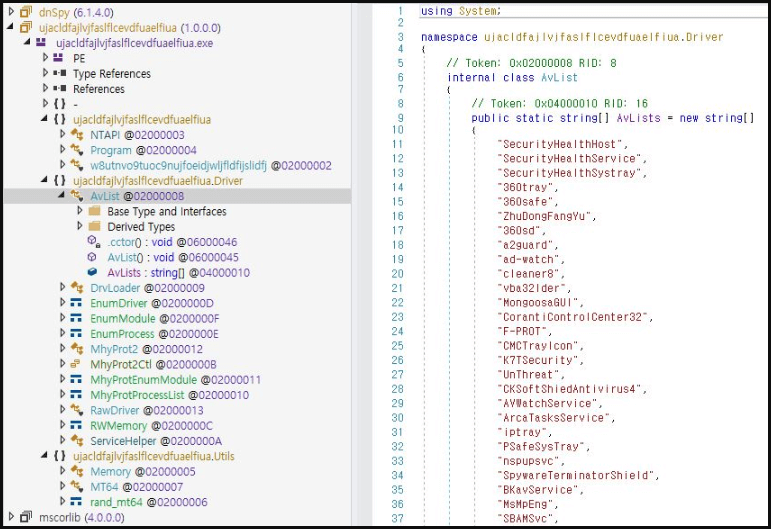
The script decodes a .NET portable executable and loads it in memory, a modified version of the Mhyprot2DrvControl open-source tool designed to exploit vulnerable Windows drivers to perform malicious actions.
As Trend Micro observed last year, Mhyprot2DrvControl specifically exploits the mhyprot2.sys file, a digitally signed anti-cheat driver for Genshin Impact.
By bypassing mhyprot2.sys, the malware can access the kernel area, ASEC explains.
The developer of Mhyprot2DrvControl provided multiple features that can be utilized with the privileges escalated through mhyprot2.sys. Unfortunately, one of these features, which allows processes to be forced to terminate, was used by the threat actor to create malware that shut down multiple anti-malware products.
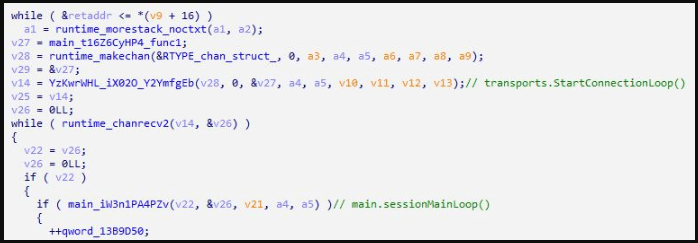
A reverse shell is used in the second part of the PowerShell script to connect to the C2 server, granting remote access to the breached device to the attacker.
According to ASEC, some Sunlogin attacks were followed by a Sliver implant (“acl.exe”). The threat actors used the implant generated by the Sliver framework in “Session Mode” without using any packers.
Alternatively, the attackers installed the Gh0st RAT for remote file management, key logging, remote command execution, and data exfiltration.
To protect against BYOVD attacks, Microsoft recommends that Windows admins enable the vulnerable driver blocklist.
According to a Microsoft support article, Windows Memory Integrity or Windows Defender Application Control (WDAC) can enable the blocklist.
A second way to defend against this attack is to block the hash of the AV killer, “f71b0c2f7cd766d9bdc1ef35c5ec1743,” and monitor event logs for newly installed services named “mhyprot2.”
If you liked this article, follow us on LinkedIn, Twitter, Facebook, YouTube, and Instagram for more cybersecurity news and topics.








